Litecoin Faces a Coordinated Attack, Cross-Chain Loss of $600,000: 'Zero-Day Vulnerability' Qualification Questioned by Security Researcher
Original Title: "Litecoin Hit by Double Spend Attack, Emergency Rollback, Security Researcher Calls Out 'Zero-Day Exploit' Claim"
Original Author: Claude, Deep Tide TechFlow
Deep Tide Summary: Litecoin experienced a coordinated attack on April 25th, exploiting the MWEB privacy layer vulnerability. The attacker performed invalid transactions through outdated nodes in about 32 minutes, executing a double spend on the cross-chain protocol, with NEAR Intents reporting a roughly $600,000 risk exposure.
The network conducted a 13-block reorganization to fix the chain state. However, security researchers discovered that this vulnerability had been privately patched 37 days ago, casting doubt on the characterization of a "zero-day attack." The official account later mocked the critics to "stay in the shallow end," sparking a strong backlash from the community.
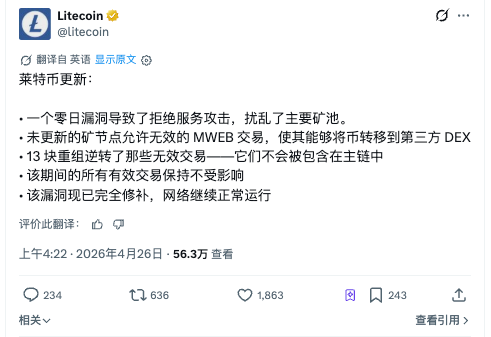
The Litecoin network experienced its first major security incident since the 2022 activation of MWEB (MimbleWimble Extension Block, Litecoin's privacy transaction layer) on April 25th. The attacker exploited a consensus bug in the MWEB layer, coupled with a denial-of-service attack on mining pools, to create a forked chain containing invalid transactions within about 32 minutes and took advantage of this window to execute double spend attacks across multiple cross-chain protocols.
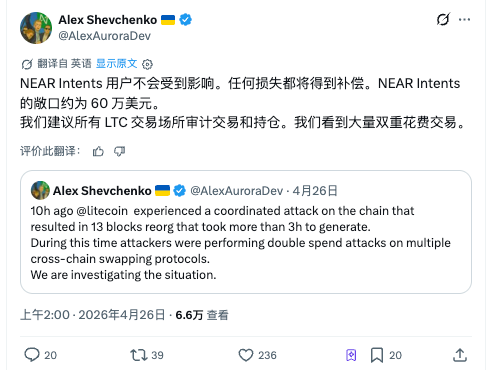
As reported by The Block on April 26th, Aurora Labs CEO Alex Shevchenko was the first to flag this anomaly on the X platform, categorizing it as a "coordinated attack" involving blocks #3,095,930 to #3,095,943, with the recovery process taking over three hours.
Attack Executed in Two Steps: Pool Disruption First, Then Exploiting Outdated Nodes
According to an official statement released by the Litecoin Foundation on April 25th, the attack path could be divided into two phases.
The first step involved launching a DoS attack on major mining pools to decrease the hash rate share of nodes running updated clients. The second step was to exploit a consensus bug in the MWEB layer by injecting an invalid MWEB transaction into nodes still running old software.
These outdated nodes incorrectly accepted the transaction as valid, allowing the attacker to "peg out" from the MWEB privacy layer (moving funds from the privacy layer to the main chain) and route the funds to a third-party decentralized exchange.
Shevchenko further revealed the attacker's on-chain traces: the attacker planned to exchange LTC for ETH, with the address used receiving funds from Binance 38 hours before the attack occurred. He inferred that the attacker had prior knowledge of the vulnerability.
Under normal circumstances, Litecoin has a block time of approximately 2.5 minutes, and 13 blocks should be produced in around 32 minutes. However, this time, the 13 blocks took over three hours to be mined, leading some observers to initially mistake this anomaly for a 51% attack.
In reality, once the DoS attack ceased, nodes running the updated code regained mining power, and the network automatically performed a 13-block reorganization to remove invalid transactions from the main chain. The Litecoin Foundation stated that all legitimate transactions during the reorganization were unaffected.
Cross-Chain Protocol Becomes Actual Victim, NEAR Intents Reports $600K Exposure
The attacker exploited the fork window period to execute double-spend transactions across multiple cross-chain swap protocols. These protocols accepted MWEB peg-out transactions that were later overturned by the reorganization, resulting in actual losses.
Shevchenko posted on Platform X stating that NEAR Intents' risk exposure is approximately $600,000, and their team will cover user losses. He also cautioned all LTC-receiving platforms to audit transaction records and holdings, as there are numerous double-spend transactions on the chain.
According to Bitcoin News, after Litecoin confirmed that the invalid transactions had been removed from the main chain, the actual settlement loss for NEAR Intents may be lower than the initial estimate. However, as of the time of publication, the protocol had not issued a follow-up statement. Other cross-chain protocols that suspended LTC-related operations are also reassessing their exposure to risks.
The Litecoin Foundation did not disclose the name of the affected mining pool or the amount of LTC that the invalid MWEB transactions attempted to generate.
Old Problem of PoW Networks: Upgrades by Volition, Security by Luck
Zcash founder Zooko Wilcox commented after the event that such rollback and double-spend attacks are not uncommon in PoW networks, with Monero and Grin having experienced similar events in recent years. In September 2025, Monero underwent its largest block reorganization in 12 years, rolling back 18 blocks and invalidating 117 transactions.
According to a CoinDesk analysis, this event exposed a structural contradiction in PoW networks: Bitcoin and Litecoin lack a mandatory update mechanism, allowing nodes to run old software indefinitely. This design has its value in the philosophy of decentralization, but it creates a fatal window when a security patch needs to reach everyone before attackers exploit vulnerabilities.
According to Yahoo Finance analysis, Litecoin's smaller hashrate and lower security budget make it more vulnerable to attacks compared to Bitcoin. Rolling back 13 blocks on the Bitcoin network would require control of over 50% of the hashrate, costing billions of dollars; however, on Litecoin, a vulnerability combined with a single DoS attack is enough to cause an equivalent-depth reorganization.
PR Disaster: Mocking Critics to "Stay in Shallow Waters," Solana Claps Back
The aftermath of the event may have caused more significant damage to trust than the attack itself.
On April 26, the official Litecoin X account posted, "Some of you know absolutely nothing about PoW, hashrate, normal operation times, reorgs, and miner/chain relationships; it's pretty obvious. Stay in the shallow end; it's safer for you there."
As reported by Bitcoin News, the post sparked hundreds of hostile replies. Users criticized its "arrogance," "immaturity," and "unprofessionalism," with some stating, "I've held your coins for years, and this is what you post?" The community expects technical transparency and post-analysis, not mockery.
The Solana official account also joined the interaction. In a discussion related to the April 25 reorg, @solana replied, "How was your weekend, kiddo?" The community interpreted this as a direct response to Litecoin's previous mocking of Solana's outage history.
As of the event disclosure, LTC was trading at around $56, dropping about 1% on the day, with a year-to-date decline of approximately 25%. The market's immediate response to the event was relatively muted.
2026 DeFi Security Quandary: Cross-Chain Infrastructure Emerges as Primary Attack Surface
According to The Block data, from 2026 through mid-April, DeFi protocols have lost over $7.5 billion due to various attacks. This includes the April 19 Kelp DAO bridge attack ($2.92 billion) and the April 1 Solana perpetual contract platform Drift attack ($2.85 billion).
Most major events have involved cross-chain infrastructure, echoing the Litecoin attacker's use of cross-chain swapping protocols to cash out.
The Litecoin incident once again demonstrates that cross-chain protocols accepting PoW chain assets face more severe confirmation issues than anticipated. When a client-side vulnerability can trigger a 13-block reorg, the question of whether 6 confirmations are secure enough is no longer theoretical.
Original Article Link
Welcome to join the official BlockBeats community:
Telegram Subscription Group: https://t.me/theblockbeats
Telegram Discussion Group: https://t.me/BlockBeats_App
Official Twitter Account: https://twitter.com/BlockBeatsAsia