Censorship Resistance of Bitcoin and Ethereum
Original title: "Censorship resistance in Bitcoin and Ethereum"
Original author: Allen Zhao, Mustafa Yilham, Henry Ang & Jermaine Wong, Bixin Ventures
Original compilation: Evan Gu, Wayne Zhang, Bixin Ventures
In early August, the U.S. Treasury Department’s Office of Foreign Assets Control (OFAC) decided to add Tornado Cash to the sanctions list The news in has put the issue of censorship resistance under the spotlight. In order to avoid related criminal liability, RPC service providers Alchemy and Infura restricted access to Tornado Cash smart contract data, and Circle (USDC issuer) also blacklisted wallet addresses on the sanction list. Blacklisted addresses are also banned by Defi protocols such as Aave, but users can still interact with some smart contracts, although many additional steps and some technical expertise are required.
This brings us to a more general question: Can blockchain be censored at the protocol level? Concerns about protocol-level censorship have emerged in the Ethereum community, with 66% of Beacon Chain validators post-merger expressing sensitivity to OFAC regulations. If more than 1/3 of validators (weighted by stake) are censored in any way, the Ethereum chain will not function properly.

In this article, we will compare the performance of BTC (POW) and ETH (POS) in anti-censorship through three key questions, and finally give our thoughts.
Definition of "censorship"
On a recent Bankless podcast, Justin Drake defined two different types of censorship: weak and strong censorship
1. Weak censorship: Weak censorship occurs when certain censored block producers do not include individual transactions in blocks, resulting in a degraded user experience. For example, a compliant block producer rejects a transaction from a blacklisted address, but the transaction is still eventually accepted by a non-censoring block producer.
2. Strong censorship: when personal transactions will never be Strong censorship occurs when included on-chain. Given that the individual has lost the ability to trade, this situation can be considered to have effectively lost the asset. This can happen when the network is taken over by a majority, also known as a 51% attack, which could threaten the continued existence of the attacked blockchain.
In the following discussion, we will separate Bitcoin and Ethereum As a representative network of POW and POS systems for comparison. We will first identify what the elements of censorship are, and then detail how Bitcoin and Ethereum achieve censorship resistance.
Issue 1: When miners/block validators are concentrated, there may be weak regulation by jurisdiction
Censorship
Bitcoin and Ethereum both face separate Centralization of mining pools and verification nodes. This could create an attack where mining pools or validator nodes could be forced to comply with regulations and censor any transactions deemed illegal within their jurisdiction.
Ethereum
Since the merger, The top two pledge service providers together hold 43.03% of the shares, and the top three hold 51.63% of the shares. The risk here is that if Lido and Coinbase join forces, they can bring the network down; if Kraken joins, the three can take over the Ethereum network.

Source: Related Network
Before we examine how Ethereum responds to the threat of centralization, let’s first introduce why validators end up becoming centralized. Under Ethereum's POS mechanism, block producers can choose which transactions are included in the next block and how they are sequenced. This allows validators to participate in the process of MEV extraction, which Amber defined very well in their recent article on ETH mergers.
“Maximum Extractable Value, also known as MEV, broadly refers to the operations to obtain residual value over a series of blocks. These operations can include reordering transactions, censoring blocks, and even attempting to reorganize the blockchain. Some common forms of MEV include sandwich attacks, arbitrage, and liquidations.”

Source: Flashbots
As shown, validator rewards increase significantly once MEV is taken into account. Due to the economic incentives brought by MEV, larger players run more validators, eliminating individual and non-professional validators. Therefore, ordinary holders are more inclined to join the verification node pool through pledge services to obtain higher and more stable income, thereby increasing the centralization of verification nodes.
Another consideration regarding stake node centralization is cryptocurrency trading platforms. The trading platform is still the best place for users to obtain Ethereum Token. Considering the huge number of users they have, many Tokens will naturally gather on these trading platforms, and the convenient benefits provided by the trading platforms through their staking platforms will attract the gathering of Tokens. We should educate users about the risks of using centralized platforms for staking, such as the possible implications if centralized platforms may choose to act maliciously due to judicial pressure.
Although the validator pool is not the most ideal solution, it will allow more ETH holders to participate , so the equity pool is still conducive to the decentralization of Ethereum.
So, how does Ethereum respond to censorship about centralization?
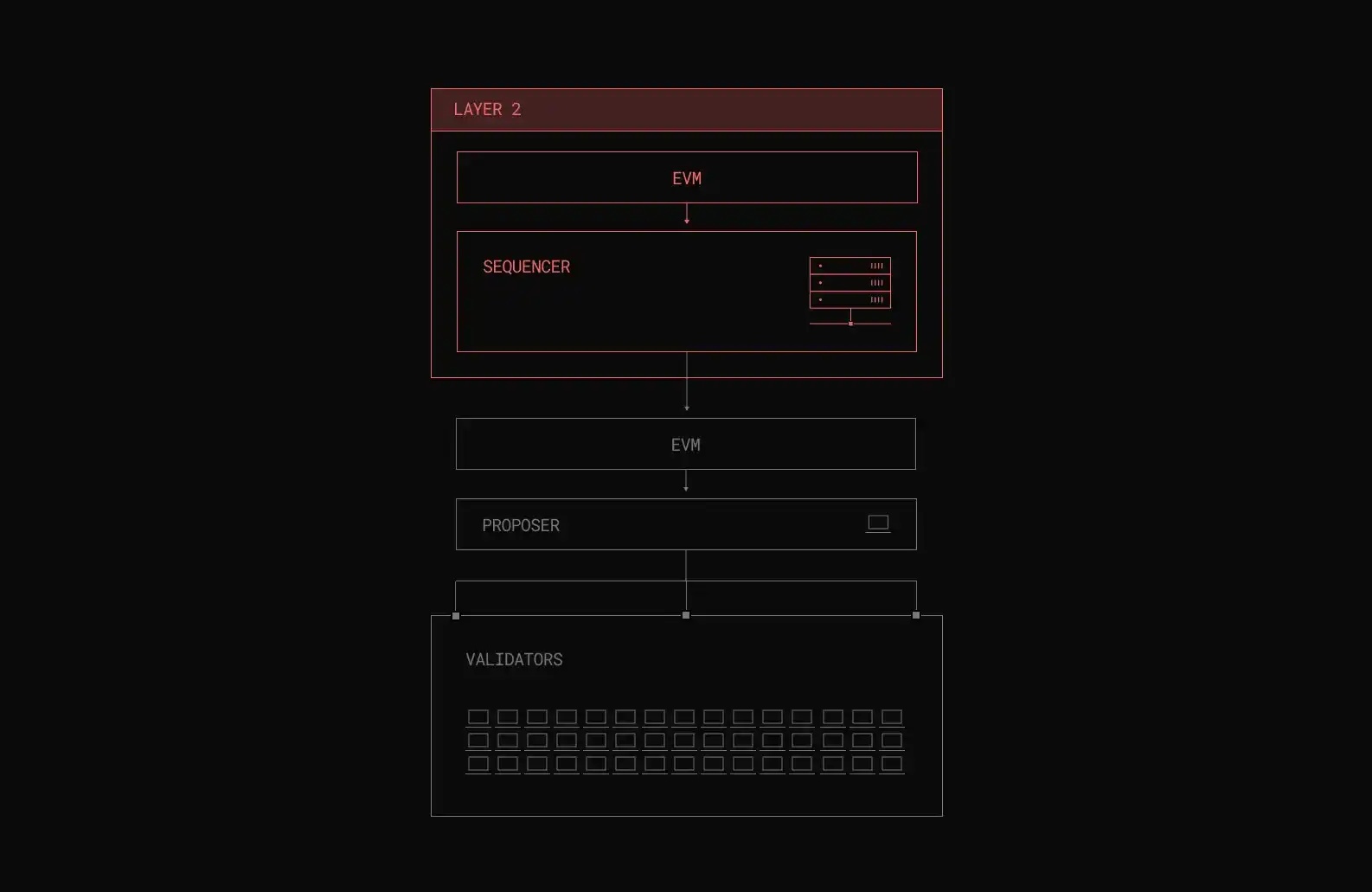
Solution 1: Separate block proposers and builders
One solution that is getting a lot of attention is Proposer Builder Separation (PBS). PBS separates the roles of block proposer and block construction, so that validators can get rewards from MEV without being complex operators, thus reducing the centralization problem.
There are three key players in the operation of the blockchain, which can check and balance each other to mitigate and ultimately eliminate potential Review.
Builders, who specialize in building blocks, extract the maximum MEV and transaction fees by ordering transactions. Afterwards, they will pay Proposers a proposal fee and put their block on-chain. Therefore, without the help of the Proposer, those builders for review purposes will not be able to publish transactions on the chain.
Proposers, also known as validators, either choose the most popular block, or they don’t Will not contain a block. If they believe a block builder is censoring transactions, they have the ability to propose a censorship resistant list (crList) that builders must include as long as the block is not full, or their block is not proposed. Since EIP-1559 has been implemented, more than 80% of blocks contain spare gas, which means that as long as users pay a priority fee above the base fee, they should be able to have their transactions included in the block. In summary, Proposers can achieve the maximum benefit by choosing the block that pays the largest amount, but still have the ability to use crList to force through the review.
The prover will monitor the block building process and will only issue a block if the proposer's block contains the highest paying block Prove it. This will prevent malicious proposers from censoring transactions.
Although the above method greatly improves the decentralization of validators, it still does not solve the problem of builders centralization problem. How to decentralize builders is beyond the scope of this discussion, but you can read more about it here .
Solution 2: Encrypted Memory Pool
< /p>
Another solution being investigated is the use of encrypted mempools to combat centralized censorship. Users encrypt transactions before broadcasting them to the mempool, and decrypt them only after they are included in an on-chain block. This will prevent any potential censors from gaining access to the contents of transactions during block construction. Additionally, it helps prevent MEV abuse such as front-running. Another benefit of a cryptographic mempool is that it can actually solve builder centralization in the future. In this case, proposers can build their own blocks by picking the highest-fee transactions from an encrypted mempool, rather than picking blocks from complex builders.
Bitcoin
Bitcoin has always been known as "digital gold" ", this feature is not only reflected in its use as a digital value storage method, but also in its resistance to censorship. Although the Bitcoin network is not as programmable as Ethereum, and weaker programmability can minimize MEV, it still faces the problem of increasing geographical concentration of miners. In addition, operating a mining machine requires professional skills, and hardware and energy are also capital-intensive. The Bitcoin mining industry has developed in the direction of resource sharing. Miners pay service fees to mines according to unit computing power, thereby reducing income Cash flow pressure brought by investment.

Source: Cambridge Bitcoin Electricity Consumption Index< p>
As the graph above shows, before China bans crypto mining in 2021, China accounts for more than 45% of the global hashrate. But the computing power has now shifted to the United States. As of January this year, the computing power of the United States has accounted for 38% of the global computing power. Mining companies may be compelled by local regulations to reject certain deals, posing a threat of scrutiny.
So, how does Bitcoin deal with the censorship issues brought about by the centralization of mining pools?
Solution 1: Switch mining pool
< /p>
Once a mining pool operator is subject to censorship regulations that are contrary to the interests of miners, miners can easily switch to other mining pools (for example, move away from the censored mining pool). Since the mode of purchasing computing power on demand is adopted, miners only need to change the address of the mining pool in the mining software to switch to a new mining pool. During 2021, when miners were banned by the Chinese government, miners were able to quickly migrate abroad and switch addresses to offshore mining pools, and the computing power has now recovered and is higher than before the ban was announced.
Although Ethereum can allow validators to withdraw or re-stake according to their will, due to the cooling period and There is still a time lag because of the queuing system.
Solution 2: Let miners have more control over the block building process< br>
Most Bitcoin miners direct their computing power to mining pools, where they use a messaging protocol called Stratum v1 to communicate with These mining pools communicate and the protocol organizes the creation and submission of hashes by miners. If mining pools collude to censor transactions, the community has no recourse. But with Stratum v2, miners will be able to choose their own transaction sets, giving them more control over the block-building process, which counters the censorship intent of malicious pool operators.
If you are interested in learning about Stratum v2 and its feature upgrades to improve miner safety and income , read here.
Solution Three: Free Market Competition
Bitcoin proponents believe that the proof-of-work mining economic incentive is the best form of resistance to any transaction censorship. As block rewards drop each halving cycle, transaction fees will tend to be 100% of miner revenue. So even if any regulatory compliant mining pool or miner scrutinizes paid transactions, other miners/pools in different jurisdictions will be more than happy to take advantage of this and steal the transaction. Ultimately, these compliant mining pools or miners will be defeated in the free market, causing their market share and profitability to decline.
Conclusion 1: Bitcoin can handle the centralization of the block creation process better than Ethereum Review questions.
Bitcoin today is much more capable of dealing with centralized censorship in the block building process. Miners can now switch pools without delay if there are pools that review certain transactions, greatly increasing miner autonomy.
While Ethereum has a viable solution to the censorship problem, it is mostly in the research phase and has not yet been implemented, Because there is competition with other programmable blockchains, other aspects of functionality need to be prioritized.
Question 2: If the security budget of the network is small, strong censorship risks may occur
< /p>
The impact of a small security budget is that it may lead to a 51% attack. When this happens, the attacker will be able to take control of the blockchain. They are able to block incoming transactions and are able to reorder new transactions. Even more serious is rewriting the history of the blockchain and reversing their own transactions, leading to double spending.
Ethereum's security budget
Once Launch a 51% attack on Ethereum, and all new deposits or withdrawals may be reviewed by the attacker, making it difficult for the network to recover. Therefore, the Token distribution in the network is decentralized as much as possible to prevent the required Token from being obtained through coercive means and attacks. At the time of writing, 13.6 million ETH is staked on the beacon chain. The economic security of Ethereum can be obtained by multiplying 13.6 million ETH by the price and multiplying by 51% to get the minimum amount required for transaction review. At the current price of $1,700 per ETH, that's about $11.5 billion in economic security today. In practice, the cost would be much higher, given that the price would rise non-linearly as demand for ETH increased.
Since taking out these funds is not a problem for some organizations or countries, we still need to consider preventive solutions.
Solution 1: Encourage more users to stake
Compared to other POS networks, only 11% of ETH is currently staked (e.g. 77% for Solana, 66% for Cosmos, 65% for Avalanche %), which means there is a lot of potential. As the stake increases, it becomes very difficult for an attacker to obtain 51% of the total stake.
However, one obstacle preventing more people from staking is the opportunity cost of DeFi benefits for users. If users can obtain better returns in DeFi, users may prioritize financial incentives, and the incentive effect of ETH pledged returns will be reduced. One of the solutions to break down the barrier is the liquid staking protocol, but this may also bring us back to the centralization problem we saw with Lido. While we can see that Lido is distributing stake to about 30 validators on its whitelist, the listing of this whitelist is still approved by Lido. Therefore, selection criteria and the ability to add and remove validators are critical, implying strong governance within DAOs.
Encouragingly, Lido has been exploring governance options using dual governance proposals, with key governance issues voted by Both stETH and LDO holders participate, which maintains consistency between both token holders. There is also a key issue related to censorship resistance, the potential to change the way stake is distributed among node operators in a potentially harmful or unintended way. In case-specific governance, once the initial proposal has been passed by LDO holders, stETH holders will also be involved, and they can also withdraw from the protocol if all available negotiations fail. Read here for a more detailed explanation of the voting mechanism and subsequent results.
Solution 2: Diversify validators to prevent coercion to gain governance rights
b>
If ETH cannot be obtained in the market, another way to gain control over the network is to forcefully win over 51% the verifier. Therefore, the censorship-resistant effect can be achieved by increasing the diversity of verifiers in the following form:
Increase diversity of jurisdictions/geography to ensure no single jurisdiction/country can take a validator offline
Increase operator/stakeholder Diversity to ensure that mandatory censorship is extremely difficult when stake is widely distributed
Increase client diversity to ensure validator clients No single bug in the end can take a validator offline
Reduced hardware requirements for participation to ensure everyone can start a validator as needed
Increase the number of validators with a complete copy of transactions
Solution 3: Societal Layer Intervention
If preventative measures fail, Ethereum Interventions will be carried out at the societal level. The specific content is to automatically execute the bifurcation process after the censorship is detected, and the system will reserve enough time for the bifurcation consensus to be reached. Ideally, a complete online node would check the memory pool to identify and identify which blockchains are censorship-oriented. Once found, they will fork and punish the censorship-purpose chains. None of these actions Intervention at the social level is required.
However, forks are rarely straightforward and quick, as censorship can sometimes be accidental, e.g. is due to a bug in the validator client. In this case, it is important to be able to intervene and discern what is real and what is accidental. In addition, there are some considerations, such as how to choose a new blockchain, which checkpoint should be taken to start the new blockchain, how to punish attackers on the new blockchain, etc., the handling of these issues will affect to the economic value of the chain. The above is to let new users understand that if they wish to participate in the new uncensored blockchain, they must first be able to withdraw funds on the chain. Although there are currently no rules and guidelines for users to understand how to respond to various policy interventions, it is very important that the governance and decision-making process of the chain should be as decentralized as possible.
Bitcoin Security Budget
If Bitcoin is subject to strong censorship, and miners will be able to mine all rewards and reorganize the chain as they see fit. Given the current hash rate of 230m TH/s, assuming that existing miners do not participate in the attack, an attacker can only control the network if they have a hash rate of more than 230m TH/s. Let's do the math, using the most efficient ASIC chip on the market today, the Antminer S19 PRO (110 TH/S), a total of 2.09 million ASIC chips (230,000,000 TH/s divided by 110 TH/s) are needed to carry out the attack. At today's price of $4,400, the total cost of acquiring the hardware to attack the network is $9 billion, before energy costs are factored in.
Solution 1: Bitcoin is more censorship resistant due to the difficulty of obtaining ASIC chips Sex
While the cost is not out of reach for some aggressive attackers, the acquisition There is a huge resistance when it comes to ASIC chips, because only a few companies can produce these ASIC chips. And since there is not enough supply coming online every year, attackers cannot launch quick attacks.
Solution 2: The conversion rate of miners is very low leading to the decentralization of the Bitcoin network
It is very difficult to obtain the machines needed to control the network, so attacks are likely to be There are mining pools to achieve this. We can solve this problem by relying on the mining pools emerging in different regions of the world, because their emergence greatly reduces the switching cost of miners, making it possible to switch quickly when facing censorship, thus achieving censorship resistance.
Conclusion 2: Bitcoin is more resilient than Ethereum in preventing strong 51% censorship attacks . Ethereum's solution of using the social layer as the last line of defense provides more power to the few, but there are still many problems with social consensus.
On the face of it, Ethereum has a higher security budget than Bitcoin. However, acquiring hardware in taking over the Bitcoin network is more of a hindrance than the cost of acquiring an Ethereum majority.
Bitcoin's solution is much simpler if an attacker takes an alternative route to a strongly censored centralized mining pool to gain control of the network, because Honest miners can help rebalance the hashrate by switching to non-aggressive pools.
In the case of strong censorship of Ethereum, although the social layer can intervene, how to transition There are still many issues with the soft fork to user activation. First, how can social consensus be achieved among non-attack participants? Can a majority of the new minority make a decision? Or is it up to the core team to decide? The decision-making process can be compared to "Ethereum DAO" voting to reach a majority decision. So should it be decided by a majority of voters or a majority stake? A common criticism in DAO voting is that a large majority of holders can vote for an outcome, only to be overruled by a single holder with a larger stake. This is not intended to reflect the actual process by which fork rules are determined, but rather to highlight problematic aspects of social governance that the Ethereum community has yet to implement. In the end, it may be that as Nic Carter said, the social consensus layer inevitably leaves room for politicization, and Ethereum may suffer the same fate as the expropriating national government.
So we think bitcoin is more resilient. It's also worth noting that this may not be the case in the future. One potential scenario is that if Bitcoin’s transaction activity fails to pick up as block rewards approach zero, the lack of transactions will result in a lack of revenue for miners who may struggle to remain solvent. This would cause miners to shut down their rigs and cause the hash rate to drop, weakening Bitcoin’s security budget. So, the Bitcoin network needs to continue to attract new users, only then it can function as a healthy network.
Question 3: External dependencies may pose a censorship risk to the underlying network
< /p>
Stablecoins
The denomination of each cryptocurrency is anchored using stablecoins, Bitcoin and Ethereum No exception. Taking a quick look at the market cap of stablecoins, we can see that the top 3 are all backed by fiat collateral held by centralized custodians. This puts them in the realm of regulation, which begs the question: what if custodians make it impossible for users to convert stablecoins to fiat simply because of government censorship or prohibition? While these are unlikely to happen, the knock-on effects are dire. Not long ago, USDC issuer Circle froze funds worth more than 75,000 USDC associated with Tornado Cash addresses in accordance with the OFAC sanctions list.

Potential Solution 1: Overcollateralized Stablecoins
One can mint a token pegged to a fiat currency in exchange for cryptocurrency collateral. MakerDAO's DAI is currently the largest decentralized stablecoin in the crypto space, and when asset prices start to fall, they maintain the 1 DAI = $1 peg by liquidating pledged crypto collateral. Since 2017, they have weathered the price swings of Bitcoin and Ethereum and have proven to be robust. However, even they have over 30% USDC exposure as part of their collateral. After the recent events with USDC and Tornado cash, they are currently having governance discussions on whether they need to implement negative interest rates to allow DAI to circulate more freely in order to realize their vision of becoming a public, neutral financial utility infrastructure.
Another option favored by Vitalik is Reflexer's RAI. In the protocol, users can deposit ETH and mint RAI up to the value of the deposited ETH. The main difference here is that RAI does not adhere to a fixed peg like the US dollar, which means that the peg of RAI changes according to the volatility of the market. They also allow for negative interest rates, which helps provide a balance where excess growth can be contained, making stablecoins less volatile. Read here for a more detailed explanation of how RAI works.
However, a fundamental problem with over-collateralized stablecoins is that they continuously extract liquidity from the market ( This is not ideal if we expect financial activity to take place on cryptocurrencies). We also have to consider what kind of collateral can be collateralized as the base currency.
Bitcoin Viability: Bitcoin is pretty much the best collateral out there. But even if there are ready-made solutions in the market, since over-collateralization will extract liquidity from the market, it is not an ideal solution if we expect financial activities to happen on-chain.
Ethereum Viability: Stablecoins using ETH as collateral may not be the way to go. If ETH faces scrutiny, these stablecoins will face redemption issues as users may want to exit their ETH positions. While using Bitcoin as collateral mitigates this associated risk, it still faces the problem of liquidity extraction.
Potential Solution 2: Algorithmic Stablecoins
Although algorithmic stablecoins are somewhat notorious due to the Luna debacle, algorithmic stablecoins are an alternative, and the goal of algorithmic stablecoins is to create a pegged stable Tokens do not require collateral, but use some form of governance Token for anchoring. The peg is then made through arbitrage opportunities between the governance token and the algorithmic stablecoin. But this kind of system design is very fragile because it requires rational participants and firm confidence in the value of governance tokens.

Once confidence is broken, a death spiral may appear: when the price of governance tokens falls, market participants not only fail to maintain the stability of token prices, but further sell their holdings of governance tokens, exacerbating the price drop .
In theory, algorithmic stablecoins could function as we do today without extracting liquidity Some parts of the banking system serve the same purpose. But there seems to be no suitable candidate project that could refine the system design of an algorithmic stablecoin, making it less risky.
Bitcoin Viability: Not applicable, there are no viable candidates in the market.
Ethereum feasibility: Not applicable, there are no viable candidates in the market.
Potential solution 3: Bitcoin or Ethereum as a decentralized stablecoin
Think: What if Bitcoin became a censorship-resistant decentralized "stablecoin"? This seems to solve the problems faced by Bitcoin and Ethereum.
Bitcoin Viability: It seems that Bitcoin holders can join, because 1 BTC = 1 BTC. This might address security budget drops due to lack of transaction activity (to recap: block reward tends to zero = all miner revenue depends on transaction fees = enough transaction activity needed to stay solvent and keep hash rate high) . If BTC is widely used on Ethereum (and any other programmable blockchain), transaction activity will come from it being a base layer currency for DeFi and many other applications, which can then maintain economic incentives for miners, further strengthening the defense against any attacks censorship resistance.
Ethereum feasibility: imagine if USDC or USDT were censored causing the chain to fork, while on the chain If there is no stablecoin linked to fiat currency, how many users will choose the stablecoin with "bubble and low transaction volume"? If Ethereum were to be used as a decentralized stablecoin, it would remove the reliance on fiat-pegged stablecoins, making chain forks a more realistic option in the face of powerful censorship attacks. Users will not have to worry about the destruction of economic value because Ethereum has strong censorship-resistant properties as a base-layer currency.
RPC Network
RPC (Remote Procedure call) network is crucial to the blockchain. It provides access to server nodes and allows users to communicate and interact with the blockchain while interacting with some stand-alone program. Given the specific hardware required to run these RPC nodes, most developers turned to centralized RPC networks such as Infura and Alchemy for their dApp API needs. The downside is that these centralized RPC networks can limit access to blockchain data if required to comply with any jurisdictional laws, and also act as a central point of failure that is vulnerable to hacking. The end result is that users may face service interruptions, greatly reducing user experience.
Solution 1: Light Client
< /p>
Ethereum has been hoping for more users to run their own light clients. Light clients do not store the full state history of the chain, but rely on sync committees to sync to the chain. They can also make arbitrary queries about the state of the network by asking other full nodes rather than through centralized Infura or Alchemy.
Bitcoin has also been encouraging users to run their own light clients. Light clients on Bitcoin can interact with the network but do not store the blockchain, and can query other nodes for blocks and transaction data of interest.
Solution 2: Decentralized RPC Network
Decentralized RPC network providers provide economic incentives for distributed RPC nodes to provide applications and users access to blockchain data. By using a decentralized set of RPC nodes, the underlying protocol layer can enhance its security and censorship resistance because there is no single point of failure. Existing solutions include Pocket Network, Ankr, and Solana's GenesysGo. Both Ethereum and Bitcoin would benefit from a decentralized RPC layer, which would improve Ethereum's censorship resistance given the large number of applications using the RPC network.
Core Developers and Project Team
The arrest of Tornado Cash founder Alexey Pertsev has sparked debate about whether developers or project teams can be held accountable for their open source code. So should they be anonymous? Easily identifiable identities place individuals within jurisdictions, which can mean they are vulnerable to regulatory control. While there is no explicit requirement that founders or developers be held accountable for their code, it may be wise to ensure that teams are geographically distributed to address any potential scrutiny from a particular jurisdiction.
Conclusion 3: External dependencies have a significant impact on the censorship resistance aspects of base layer protocols.
We think the first problem to be solved is the choice of base layer currency, Bitcoin and Ethereum The economic value is all pegged to USDC and USDT which are vulnerable to US regulations. For other possible sources of censorship risk including RPC layer and protocol developers, we believe existing solutions can mitigate and eventually eliminate these issues.
Conclusion
Although we have made extensive comparisons between Bitcoin and Ethereum, they also have their own characteristics and solutions in terms of censorship resistance, such as the characteristics of Bitcoin Making it work for base layer currencies, but we still need the programmability of blockchains like Ethereum to have on-chain applications. At the end of the day, the qualities of decentralization, censorship resistance, and sovereign independence are what Bitcoin, Ethereum, and many other blockchains are all trying to achieve.
This article is from a contribution and does not represent the views of BlockBeats.
Welcome to join the official BlockBeats community:
Telegram Subscription Group: https://t.me/theblockbeats
Telegram Discussion Group: https://t.me/BlockBeats_App
Official Twitter Account: https://twitter.com/BlockBeatsAsia